Đối tác của +500 thẩm mỹ viện, phòng khám da liễu
Công ty TNHH Thiết bị Thẩm mỹ và Công nghệ Y học (BEMED) là đơn vị chuyên nhập khẩu và phân phối độc quyền các thiết bị thẩm mỹ chính hãng công nghệ cao. Từ 2012 đến nay, BEMED đã là đối tác chiến lược của hơn 500 bệnh viện thẩm mỹ, spa, phòng khám da liễu tại Việt Nam.
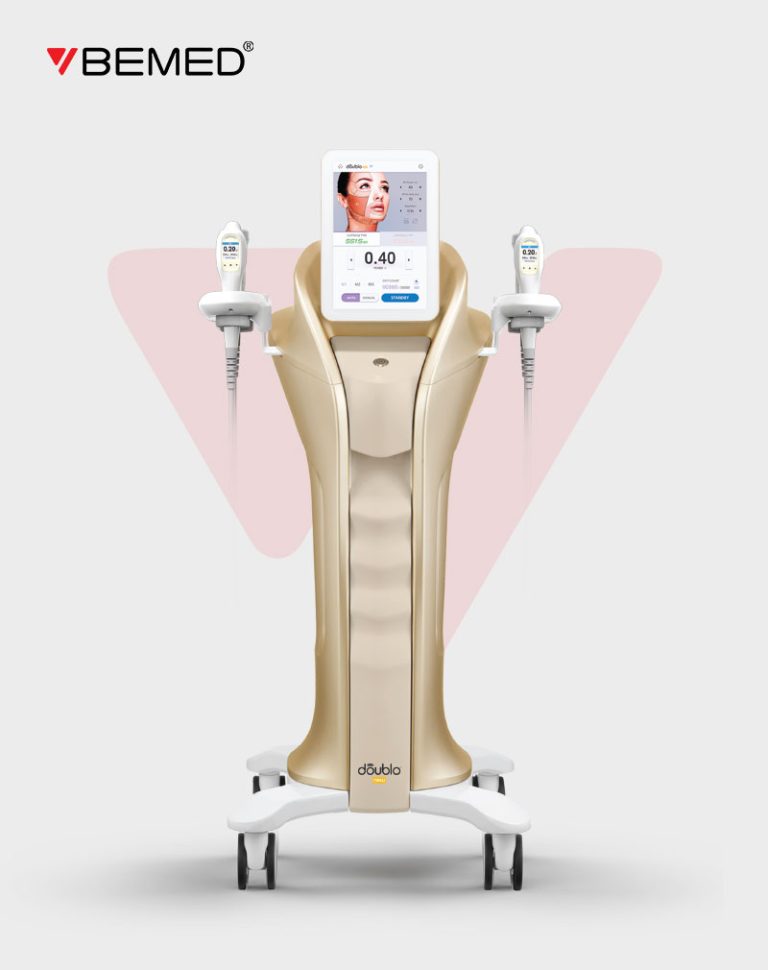
Thiết bị thẩm mỹ Chính hãng
Là đối tác phân phối độc quyền chính hãng thiết bị thẩm mỹ của các thương hiệu hàng đầu như WONTECH, HIRONIC, NOVAVISON,...
Công nghệ tiên tiến - an toàn
Thiết bị thẩm mỹ công nghệ cao, đã được các chuyên gia hàng đầu kiểm chứng lâm sàng và thông qua các tiêu chuẩn quốc tế về an toàn và hiệu quả như FDA, CE, KFDA,...
chính sách hậu mãi hấp dẫn
Cùng với bảo hành chính hãng của từng thiết bị, BEMED hỗ trợ kỹ thuật cho phòng khám 24/7. Khách hàng cũng sẽ nhận được gói hỗ trợ Marketing về công nghệ thẩm mỹ đi kèm với mỗi thiết bị.
Quy trình Chuyển giao - đào tạo
Quy trình chuyển giao công nghệ thẩm mỹ tại BEMED tuân thủ theo Luật số: 07/2017/QH14 – Điều 6 Luật Chuyển giao công nghệ 2017:
1. Chuyển giao tài liệu
BEMED chuyển giao toàn bộ tài liệu về công nghệ và thiết bị cho bên nhận. Bộ tài liệu gồm: Hướng dẫn sử dụng, lắp đặt kỹ thuật và các lưu ý trong điều trị, hướng khắc phục.
2. Đào tạo công nghệ
Chuyên gia về công nghệ thẩm mỹ của BEMED sẽ đào tạo trực tiếp cho bác sĩ, chuyên viên điều trị thẩm mỹ nắm vững và làm chủ công nghệ trong thời hạn thỏa thuận.
3. Đào tạo ứng dụng
Chuyên gia kỹ thuật thiết bị thẩm mỹ của BEMED tiến hành đào tạo và tư vấn cho phòng khám cách ứng dụng theo nhu cầu trị liệu cụ thể và cách vận hành thiết bị. Đảm bảo các chỉ tiêu về chất lượng sản phẩm, tiến độ theo thỏa thuận.
4. Hoàn tất chuyển giao
BEMED chuyển giao đầy đủ máy móc, linh kiện; bí quyết công nghệ; phương án, quy trình; giải pháp, thông số kỹ thuật; giải pháp Marketing về công nghệ cho phòng khám.
5. Hỗ trợ sau chuyển giao
Sau khi hoàn tất quá trình chuyển giao, đội ngũ chuyên gia kỹ thuật và công nghệ thẩm mỹ của BEMED sẽ duy trì chăm sóc và hỗ trợ về kỹ thuật, bảo trì thường xuyên thiết bị cho phòng khám.
CHỨNG THỰC






500+ KHÁCH HÀNG